Intrusion Definition
ĭn-tro͝ozhən
intrusions
noun
intrusions
The act of intruding.
Webster's New World
The illegal entering upon another's property without right to possession.
Webster's New World
An inappropriate or unwelcome addition.
American Heritage
Webster's New World
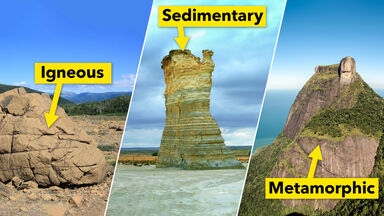
The invasion, as of liquid magma, into or between solid rock.
Webster's New World
Synonyms:
Other Word Forms of Intrusion
Noun
Singular:
intrusionPlural:
intrusionsOrigin of Intrusion
From Old French intrusion, from Medieval Latin intrusio
From Wiktionary
Find Similar Words
Find similar words to intrusion using the buttons below.