Accountability Definition
The state of being accountable; liability to be called on to render an account; accountableness; responsible for; answerable for.
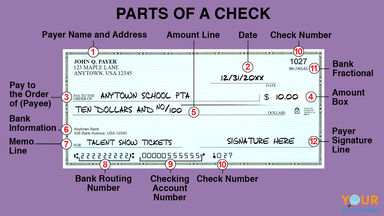
(military) The obligation imposed by law or lawful order or regulation on an officer or other person for keeping accurate record of property, documents, or funds. The person having this obligation may or may not have actual possession of the property, documents, or funds. Accountability is concerned primarily with records, while responsibility is concerned primarily with custody, care, and safekeeping. (JP 1-02 Department of Defense Dictionary of Military and Associated Terms)
Other Word Forms of Accountability
Noun
Origin of Accountability
-
From accountable +"Ž -ity.
From Wiktionary
Accountability Is Also Mentioned In
Find Similar Words
Find similar words to Accountability using the buttons below.